Cryptographic Hash Properties
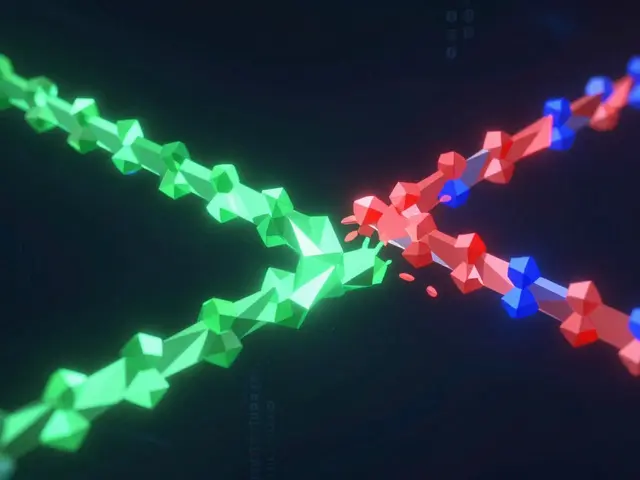
When working with cryptographic hash properties, the set of security characteristics that define how a hash function behaves. Also known as hash function attributes, they determine a hash’s usefulness in blockchain, password storage, and data integrity. A hash function that meets strong collision resistance, the difficulty of finding two different inputs that produce the same output and robust pre‑image resistance, the challenge of reversing a hash to its original input can protect against forgery and replay attacks. These two traits, together with second pre‑image resistance, the effort required to find a different input that hashes to an existing output, form the core of what we call cryptographic hash properties. For example, SHA‑256, a widely used hash algorithm in Bitcoin and many other systems offers high pre‑image resistance, making it a go‑to choice for proof‑of‑work mining. cryptographic hash properties are not just academic; they decide whether a digital signature can be trusted or whether a simple checksum is enough. The properties also include determinism (the same input always yields the same output) and the avalanche effect (a tiny change in input flips many output bits), both of which are essential for predictable yet unpredictable behavior.
Why These Properties Matter
In practice, every secure protocol leans on these properties. A blockchain that relies on collision resistance ensures that no attacker can create an alternate block with the same hash, preserving the immutable ledger. When a password manager stores hashes, it depends on pre‑image resistance so that stolen hash values cannot be turned back into plain passwords. Likewise, digital certificates use second pre‑image resistance to prevent an adversary from crafting a different certificate that matches the original hash, which would break trust chains. Merkle trees, a staple of many distributed ledgers, exploit the deterministic nature of hash functions to create compact proofs of inclusion; each node’s hash inherits collision and pre‑image resistance from its children, making the whole structure tamper‑evident. These relationships show that cryptographic hash properties enable data integrity, authentication, and non‑repudiation across many applications.
Below you’ll find articles that unpack each of these traits, compare popular hash algorithms, and explain how real‑world systems like Bitcoin mining, smart‑contract checksums, secure file storage, and API request signing make use of them. One guide walks through the math behind collision resistance and why a 256‑bit hash makes brute‑force attacks impractical. Another article reviews SHA‑256, SHA‑3, and BLAKE2, highlighting their pre‑image and second pre‑image resistance scores. There’s also a practical piece on choosing the right hash for password hashing, covering salt, pepper, and key‑stretching techniques. Whether you’re a developer building a new DeFi protocol, a security analyst auditing a legacy system, or just curious about why hash functions matter, the collection ahead gives you concrete examples, actionable tips, and the latest insights on picking the right hash for your needs.

Cryptographic Hash Properties Essential for Blockchain
Learn why cryptographic hash functions are crucial for blockchain security, covering essential properties, popular algorithms, and practical implementation tips.
Read More