Public Key Cryptography: How Secure Crypto Transactions Really Work
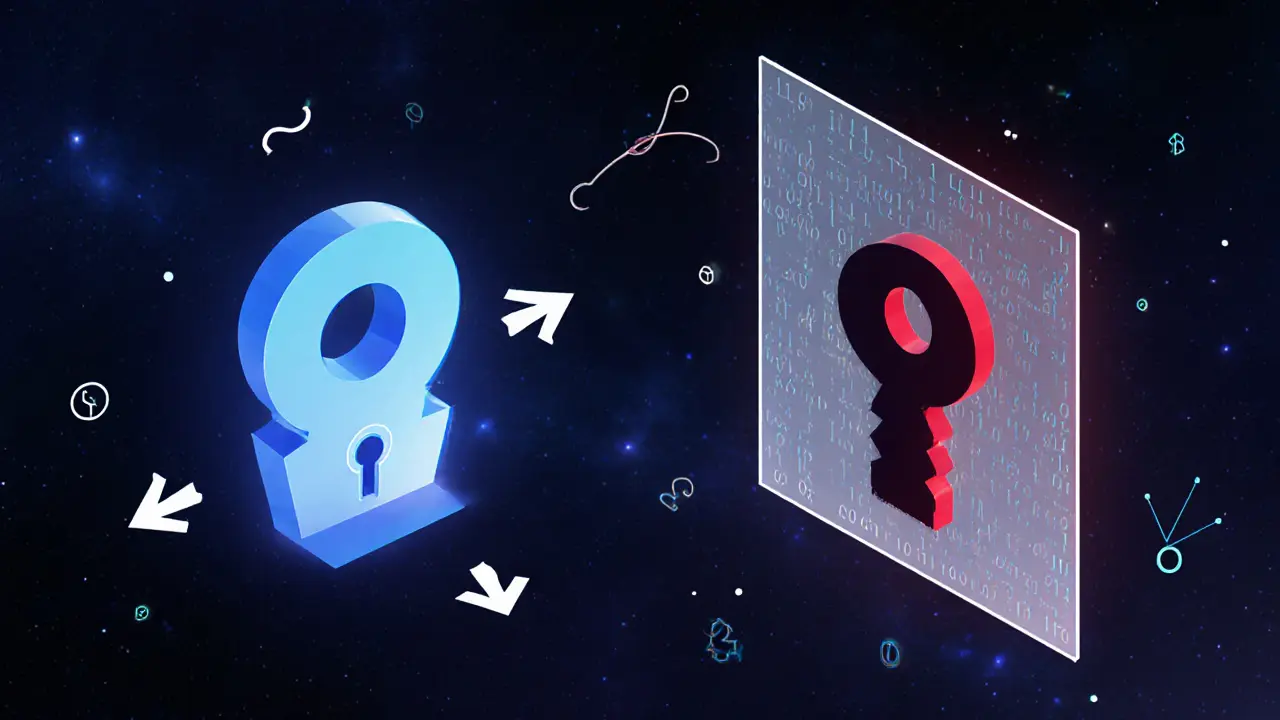
When you send Bitcoin or sign a DeFi transaction, you're using public key cryptography, a system that uses two mathematically linked keys—one public, one private—to prove identity and secure data without sharing secrets. Also known as asymmetric encryption, it’s the invisible guardrail behind every crypto wallet, exchange, and smart contract. Unlike old-school passwords, where one key locks and unlocks everything, this system splits the job: your private key stays locked in your device, while your public key is shared openly. Anyone can send you crypto using that public key, but only your private key can unlock it. No middleman. No shared secrets. Just math.
This isn’t just theory—it’s what makes digital signatures, a cryptographic proof that ties a message or transaction to a specific private key possible. When you sign a transaction on Ethereum or verify ownership of an NFT, you’re generating a unique digital fingerprint only your private key can create. Blockchains check that fingerprint against your public key. If it matches, the transaction is valid. This is why you can’t fake a withdrawal from someone else’s wallet—even if you know their address. And it’s why exchanges like BitHash or Coinsuper fail when they try to control your keys: they break this system. The same logic applies to blockchain voting, where each vote is signed with a private key to ensure authenticity and prevent tampering. If the signature doesn’t match the public key on record, the vote gets rejected.
Public key cryptography doesn’t just protect money—it enables trust in systems with no central authority. That’s why privacy coins like Monero and Zcash rely on advanced variants of it to hide transaction details while still proving they’re valid. It’s also why KYC and AML rules are struggling to catch up: these systems were built to work without knowing who you are. Even when governments try to ban privacy coins, they can’t break the math. The same math protects your wallet from scams like the fake WKIM Mjolnir airdrop or the MOON token scam. If you didn’t sign it with your private key, it’s not yours. And if someone stole your private key, no amount of regulation can bring it back.
What you’ll find below isn’t a textbook. It’s real-world proof of how public key cryptography shapes the crypto world—sometimes successfully, sometimes dangerously. From how block structure relies on cryptographic hashing to why Indonesian exchanges must verify digital signatures under new licensing rules, every post here connects back to this one core idea: your keys, your crypto. Understand it, and you stop guessing. You start knowing.
How Public Key Cryptography Keeps Bitcoin Secure
Public key cryptography is the backbone of Bitcoin's security, using math to prove ownership without trusted third parties. Learn how private keys, ECDSA, and Schnorr signatures keep Bitcoin safe.
Read More