secp256k1: The Crypto Math Behind Bitcoin and Ethereum
When you send Bitcoin or Ethereum, secp256k1, a specific elliptic curve used to generate cryptographic keys. It's also known as Koblitz curve, and it's the quiet hero making sure only you can spend your crypto. Without it, your wallet wouldn't be secure — anyone could steal your coins. This isn't just theory; it's the exact math Bitcoin and Ethereum use every second to sign transactions and verify ownership.
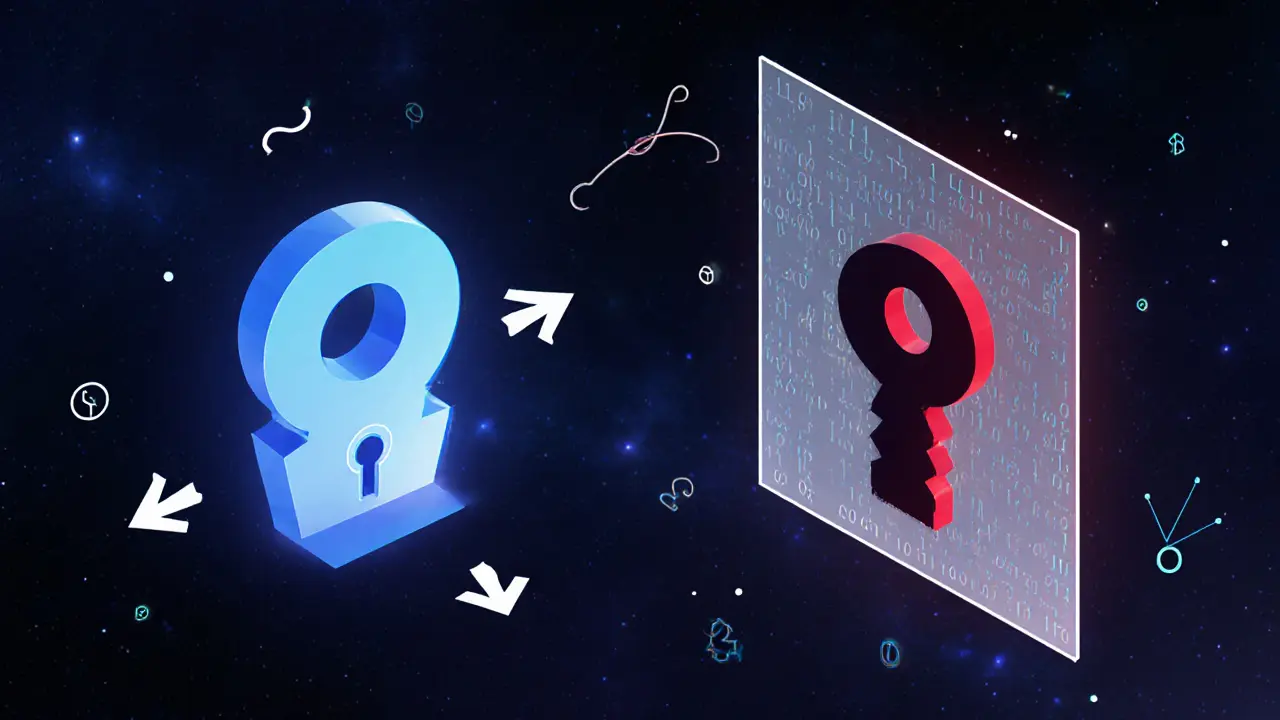
secp256k1 works by turning a random number into a public key you can share — while keeping the private key locked away. Think of it like a lock and key: you give out the lock (public key), but only you have the key (private key). That’s how your wallet address is created. This curve is special because it’s fast, simple, and resistant to attacks. Unlike other curves, it was chosen for Bitcoin back in 2009 because it’s computationally efficient — meaning it doesn’t drain your phone’s battery when signing a transaction. And it’s still used today by Ethereum, Litecoin, and dozens of other blockchains.
But secp256k1 doesn’t work alone. It teams up with elliptic curve cryptography, the mathematical system that makes digital signatures possible to create what’s called ECDSA — the signature algorithm that proves you own your coins. When you sign a transaction, you’re using secp256k1 to generate a unique proof that can’t be forged. That’s why even if someone sees your public address, they can’t fake your signature. And because it’s deterministic — the same message always produces the same signature — it’s also audit-friendly. Regulators and auditors can trace transactions without needing your private key.
Some people confuse secp256k1 with encryption, but it’s not used to hide data. It’s used to prove identity. That’s why it’s perfect for crypto: you don’t need to keep secrets hidden — you just need to prove you’re the one who owns them. This is why even when exchanges get hacked, your coins stay safe as long as your private key isn’t stolen. The curve itself isn’t broken. The weakness is always human — bad passwords, phishing, or careless wallet storage.
And it’s not going away. Even as new technologies like Schnorr signatures and zk-SNARKs roll out, they still rely on secp256k1 as their base. It’s the foundation. You can’t upgrade the house without fixing the foundation first. That’s why every crypto wallet, hardware or software, uses this curve. It’s not a trend — it’s the standard.
Below, you’ll find real-world examples of how secp256k1 shows up in crypto scams, exchange failures, and regulatory crackdowns. Some posts show how bad actors try to fake signatures. Others reveal how exchanges mess up key generation — and what happens when they do. You’ll see why some tokens fail because their smart contracts use flawed implementations of this same math. This isn’t just about theory. It’s about the hidden code that keeps your money safe — or lets it slip away.
How Public Key Cryptography Keeps Bitcoin Secure
Public key cryptography is the backbone of Bitcoin's security, using math to prove ownership without trusted third parties. Learn how private keys, ECDSA, and Schnorr signatures keep Bitcoin safe.
Read More