Bridge Security for Wrapped Tokens: How to Protect Your Assets
Imagine locking your gold bars in a vault in New York and receiving a digital receipt in London that is worth exactly the same amount and can be traded just like gold. That is essentially how wrapped tokens work. But what happens if someone steals the gold from the New York vault while you still hold the receipt? Suddenly, your digital asset is just a worthless piece of code. This is the core risk of bridge security, and it is where some of the biggest losses in crypto history have happened.
To understand the danger, we first need to define the mechanism. Wrapped Tokens are digital assets that represent a blockchain asset locked on its native chain, allowing it to be used on a different blockchain. For instance, if you want to use your Bitcoin on the Ethereum network to earn interest, you use a bridge. The bridge locks your BTC and mints an equivalent amount of WBTC (Wrapped Bitcoin) on Ethereum. This process unlocks massive liquidity and lets you jump between different DeFi ecosystems without selling your original coins.
The Mechanics of the Vault and Mint System
Most bridges use a "lock-and-mint" architecture. When you move an asset, it doesn't actually "travel" between chains-that's technically impossible. Instead, the asset is deposited into a vault on the source chain. Once the bridge confirms the deposit, it mints a synthetic version of that asset on the target chain.
For a bridge to be secure, the ratio of locked assets to minted tokens must always be 1:1. The bridge operator acts as the custodian. To prevent a single point of failure, modern bridges avoid keeping all funds in one place. A robust setup, like the one used by ChainPort, utilizes a split storage strategy. They keep only a tiny fraction of assets in "hot wallets" for immediate liquidity and move the bulk of the funds into cold storage. These cold vaults are typically secured by MPC (Multi-Party Computation), a technology that splits a private key into multiple pieces so no single person can authorize a withdrawal.
| Storage Type | Accessibility | Security Level | Primary Use Case |
|---|---|---|---|
| Hot Wallet | Instant | Low | Fast user withdrawals |
| Multi-Sig (Gnosis Safe) | Moderate | High | Administrative actions |
| MPC Cold Storage | Slow | Very High | Long-term asset backing |
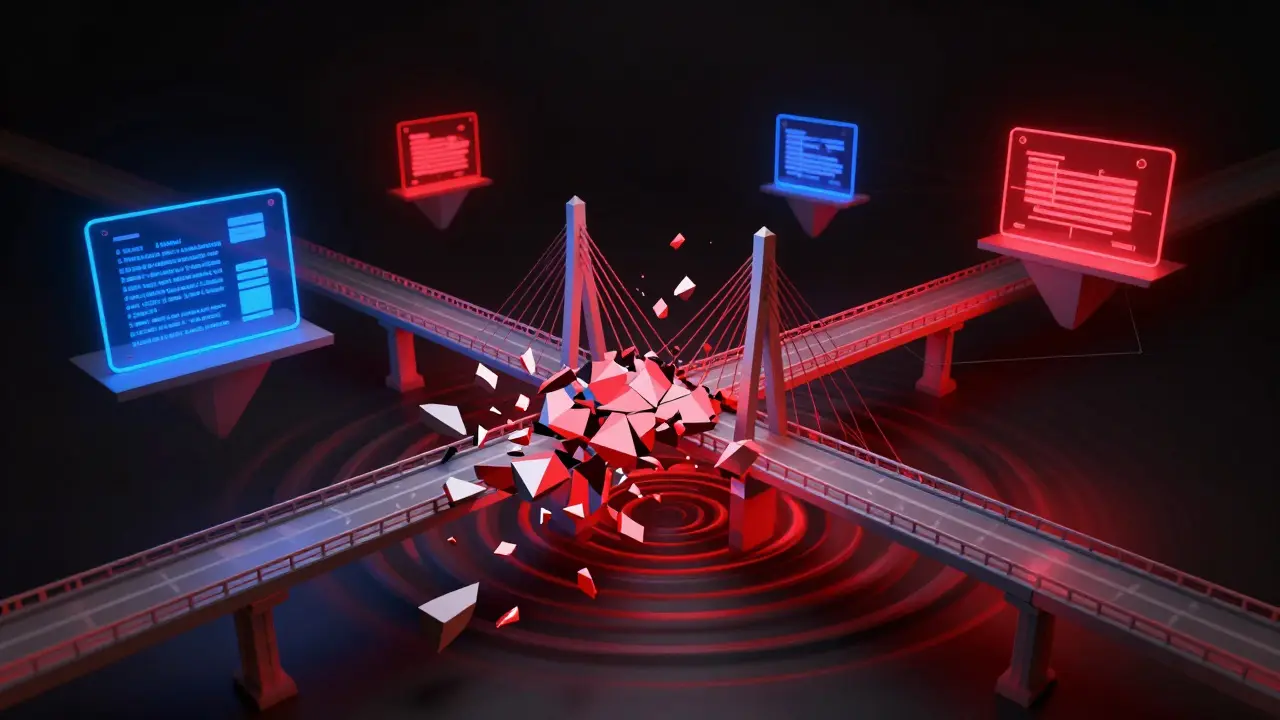
Two Nightmare Scenarios: Collateral Drainage and Infinite Minting
When bridges fail, they usually fall into one of two traps. The first is the Collateral Drainage attack. In this scenario, a hacker finds a way to withdraw assets from the source vault without actually burning the wrapped tokens on the target chain. If the BTC is gone from the vault but the WBTC still exists, the wrapped token is no longer backed by anything. It becomes a "naked" token, and its value usually crashes toward zero because the trust is broken.
The second is the Infinite Mint exploit. This is the opposite problem. A bug in the smart contract allows an attacker to mint new wrapped tokens out of thin air without depositing any collateral. Imagine if a bank suddenly printed a billion dollars and gave it to one person. The market would be flooded with these tokens, and the attacker could dump them on decentralized exchanges, draining the liquidity pools and leaving legitimate holders with assets that have no real-world value.
The Ripple Effect on DeFi Protocols
Bridge security isn't just a problem for the person crossing the bridge; it's a systemic risk. Many DeFi Protocols are financial applications built on blockchain that remove intermediaries by using smart contracts. These protocols often accept wrapped tokens as collateral for loans.
If a bridge is exploited and the wrapped token loses its value, the lending protocol suddenly holds "bad debt." If the collateral (the wrapped token) is worth nothing, the protocol cannot recover the funds it lent out. This can lead to total insolvency. This means you could be lending native ETH in a pool and still lose money because someone else used a compromised wrapped token as collateral in that same pool. The contagion spreads quickly across the ecosystem.
Evaluating Smart Contract Safety
Since bridges rely on code, the code must be flawless. A single logic error in the "unwrap" function can lead to a total loss of funds. This is why Smart Contract Audits are non-negotiable. An audit isn't just a "stamp of approval"; it's a rigorous stress test where third-party experts try to break the code. They look for common vulnerabilities like reentrancy attacks or integer overflows.
When checking a bridge, don't just look for the word "audited." Look for the actual public report. A transparent project will list every vulnerability found and show exactly how they fixed it. If a project claims to be secure but hides its audit reports, that is a massive red flag.
How to Manage Your Own Risk
If you are using wrapped tokens, you are essentially trusting the bridge operator. To minimize your exposure, follow these rules of thumb:
- Diversify your bridges: Don't put all your assets through a single bridge provider.
- Check the backing: Look for bridges that provide real-time proof of reserves, showing that the assets in the vault match the tokens minted.
- Use insurance: Some platforms now offer insurance coverage. While not perfect, it provides a safety net if the bridge is compromised.
- Prefer decentralized MPC: Avoid bridges that rely on a single private key held by one person. Look for those using Fireblocks or Gnosis Safe.
The trade-off is always between convenience and security. Single-transaction bridging is great for user experience because it eliminates the need to manually release transactions on the target chain, but it often requires slightly more gas on the source chain to handle the automation. For most users, this small cost is worth the reduction in manual errors.
What happens if the bridge that issued my wrapped tokens is hacked?
If the collateral in the source vault is stolen, your wrapped tokens may lose their value because they are no longer backed 1:1 by the original asset. Depending on the bridge, you might be able to claim a portion of the remaining assets, or you might be left with a worthless token.
Is WBTC safer than using a bridge myself?
WBTC uses a centralized custodian model where professional entities hold the BTC. While this is a form of trust, it is often considered more stable than smaller, automated bridges that rely solely on smart contracts which might have undiscovered bugs.
What is the difference between a hot wallet and a cold wallet in bridging?
A hot wallet is connected to the internet and allows for fast, automated transactions. A cold wallet is offline, making it nearly impossible to hack remotely. Secure bridges keep the majority of user funds in cold storage and only a small amount in hot wallets for daily operations.
Can a smart contract audit guarantee 100% security?
No. An audit reduces risk by finding known vulnerabilities, but it cannot guarantee that no bugs exist. It is a snapshot of security at a specific point in time. Continuous monitoring and bug bounty programs are also necessary.
Why are wrapped tokens useful if they carry this risk?
They provide essential interoperability. Without them, your Bitcoin is stuck on the Bitcoin network. Wrapping allows you to use that value in Ethereum's DeFi ecosystem to earn yield, provide liquidity, or take out loans, which would otherwise be impossible.





23 Comments
Shannon Kelly Smith
April 19, 2026 at 09:40
This is such a great breakdown for anyone getting into DeFi! 🚀 Understanding the lock-and-mint process is honestly the only way to stay safe in this wild market. Keep learning and stay curious! 💎🙌
Joshua Salwen
April 20, 2026 at 02:02
OMG finally someone mentions this!! People are just blindly throwing money into these bridges like it's a slot machime and then they act suprised when their funds vanish into thin air!! It's absolutley insane how many people don't even know what a hot wallet is!! Totaly reckless!!
John and Lauren Busch
April 20, 2026 at 20:57
Wow, a 1:1 ratio. Truly revolutionary stuff here.
Michelle Stanish
April 22, 2026 at 07:49
I dont trust any bridge.
Sean Mitchell
April 23, 2026 at 07:33
The sheer audacity of the industry to call these "security measures" while millions are drained every other week is simply breathtaking. It's a farcical masquerade of stability!
Luke George
April 24, 2026 at 05:56
You think these audits are real? Give me a break. They're all paid for by the projects themselves to create a false sense of security while the elites keep the backdoors open. It's all part of the same system to control liquidity and flush out the retail traders before the big reset happens. Don't be fooled by the "MPC" buzzwords, it's just another way to hide who actually holds the keys.
Gillian Kent
April 24, 2026 at 17:26
I tried using one of these and the interface was so confussing, almost lost everything because i didnt read the ffine print about gas fees. Just be careful out there guys, the tech is cool but the exeperience is messy
Michael Harms
April 26, 2026 at 04:23
Really appreciate the tips on diversifying bridges! It's like not putting all your eggs in one basket, right? Definitely a smart move for anyone looking to grow their portfolio safely. Cheers for the guide!
Abhinav Chaubey
April 26, 2026 at 14:55
Actually, the MPC implementation mentioned here is basic knowledge for any serious developer. My country is leading the way in blockchain engineering and we see these vulnerabilities long before they hit the Western markets. The "Infinite Mint" is just a failure of basic logic that any competent programmer would avoid if they weren't rushing for a VC seed round.
Jeff Barlett
April 27, 2026 at 17:47
Who cares about audits? Every "audited" project I've ever touched has crashed anyway. It's all a scam to make you feel safe while they rug you from the inside out. Absolutely pathetic that we still believe in these reports.
Sandeep Bhoir
April 29, 2026 at 11:15
Right, because an audit totally guarantees you won't get hacked. Brilliant.
Thomas Jewett
April 30, 2026 at 01:06
It is a disgrace that we let these offshore entities handle our wealth with such lax standartz. If this were managed by real American firms with actual accountability and patriotic oversight, we wouldn't be seeing these blatant thefts of our hard-earned money by foreign actors who have no respect for the law or the individual propety rights we hold dear in this great nation!!
Anna Grealis
May 1, 2026 at 14:33
the whole thing is a lie. they probably just fake the proof of reserves using flash loans and we just eat it up. typical.
Karen Mogollon Gutierrez
May 2, 2026 at 12:40
It is truly an egregious oversight that most users neglect to perform their own due diligence. One must ascertain the veracity of the audit reports through independent verification, lest they find themselves in a position of absolute financial ruin!
Tracy Sperandio
May 4, 2026 at 09:06
Let's get pumped about this! 🌟 Understanding the guts of the system is how we win. Grab your assets, secure them like a fortress, and let's ride this bull run into the stratosphere! Knowledge is the ultimate power-up! ⚡️
Ankit Sindhu
May 4, 2026 at 22:01
For those who are confused about the 1:1 ratio, think of it as a gold certificate. If the gold is gone, the paper is just paper. I'm here to help if anyone needs a simpler explanation of the MPC part.
Robert Preston
May 6, 2026 at 20:51
If you're feeling overwhelmed, just start by moving your assets to a cold wallet first. The automation of single-transaction bridging is convenient, but taking an extra ten minutes to verify your transaction on the target chain can save you from a lifetime of regret.
Kevin Lư
May 7, 2026 at 08:43
Man, I just want a bridge that works without me having to read a whole thesis on MPC. Why is crypto so hard? Just let me move my coins, man.
Chintu Parikh
May 9, 2026 at 00:39
I humbly suggest that we all collaborate to create a standardized checklist for bridge safety. It would be an honor to contribute to such a noble cause for the benefit of the entire community, ensuring that no novice investor falls prey to these technical pitfalls.
Alex Long
May 9, 2026 at 11:24
Too long. Just says "don't use bridges" in 500 words. Boring.
Nishant Goyal
May 11, 2026 at 04:22
Good info. Stay safe everyone.
Gaurav Undirwade
May 12, 2026 at 10:24
It is an absolute travesty that such primitive errors as "integer overflows" are still occurring in the modern era. Those who fall for these traps simply lack the moral discipline to study the code themselves before risking their wealth. One must be rigorous or suffer the consequences of their own ignorance.
Mike Kempenich
May 13, 2026 at 09:54
I think we can really push the industry toward better standards if we keep discussing this. It's all about incremental improvement and staying positive about the tech while staying cautious about the implementation!